Why AI for Accounting Is No Longer Optional
AI for accounting transforms how firms handle data entry, financial reporting, and client advisory work. It automates repetitive tasks, reduces errors, and frees accountants to focus on strategic decision-making. Here’s what you need to know:
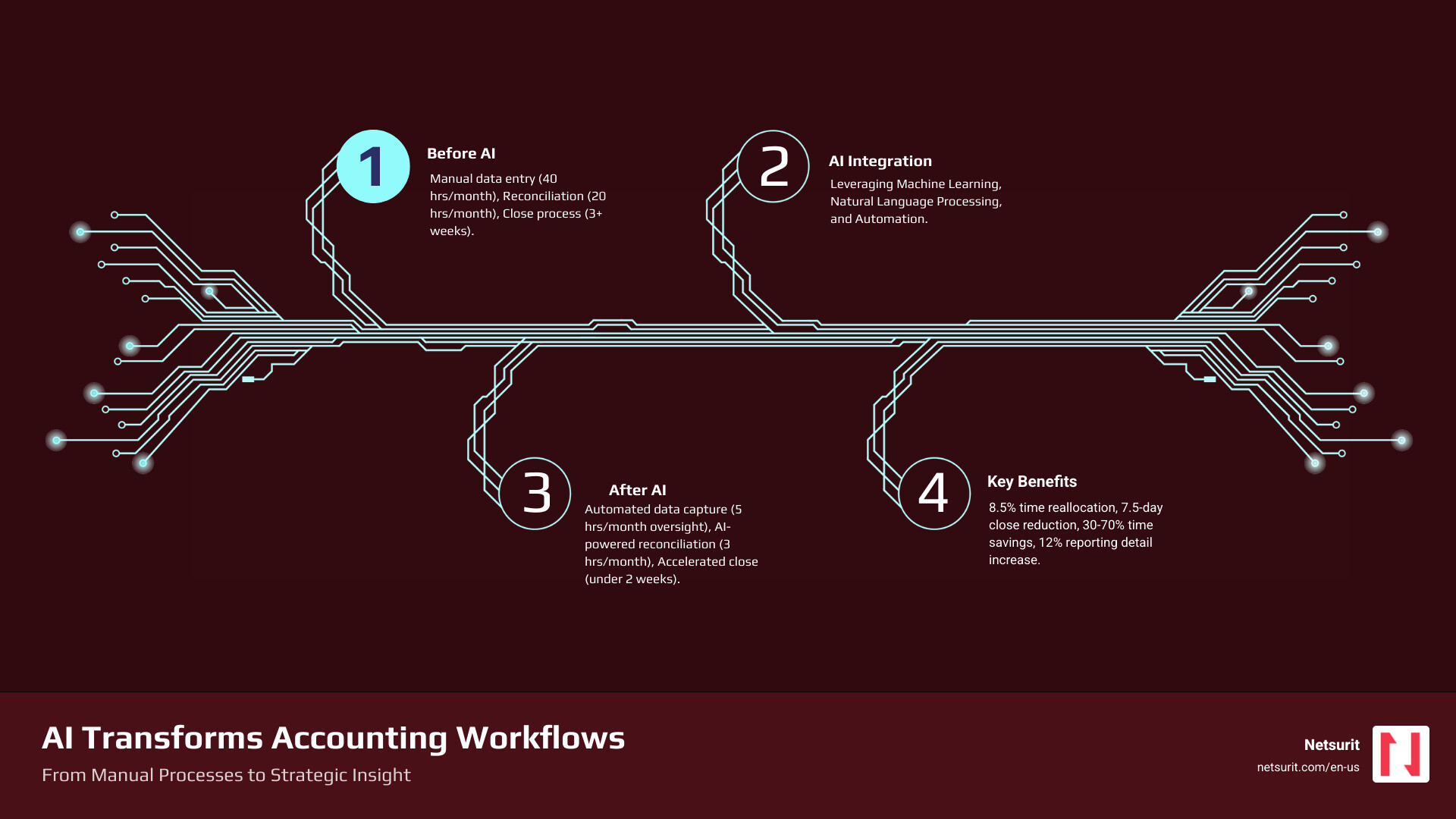
- Efficiency: AI reallocates approximately 8.5% of accountant time from data entry to high-value tasks
- Speed: Firms using AI see a 7.5-day reduction in monthly close time
- Accuracy: AI detects patterns and anomalies humans often miss, lowering fraud risk
- Growth: Accountants report increased client capacity and job satisfaction when AI handles routine work
The accounting profession faces three converging pressures: a deepening talent shortage, rising regulatory complexity (think ESG disclosures and evolving lease standards), and the persistent risk of manual errors that cost firms both money and reputation. AI for accounting addresses all three simultaneously. It’s not a speculative technology—it’s a practical solution already delivering measurable productivity gains across firms of every size.
The shift is dramatic. Only 21% of tax firms currently use generative AI, but 53% are actively planning or considering adoption. Among early adopters, the results speak clearly: 30–70% time savings on workflow automation, 50% faster document analysis for research, and firms finalizing monthly financial statements almost two weeks sooner than competitors still relying on manual processes.
Yet adoption brings real challenges. Integration with legacy systems tops the list of obstacles, followed by security concerns, data governance questions, and the skills gap between what AI can do and what accountants know how to ask of it. The most successful implementations pair AI’s computational power with human judgment—what researchers call the “human-in-the-loop” model. AI handles the pattern recognition and first-pass analysis; experienced accountants interpret the results, apply business context, and make the final call.
This guide unpacks how AI works in accounting, where it delivers the highest ROI, what risks you must manage, and how to build a phased adoption plan that fits your firm’s size and risk tolerance. You’ll see concrete examples from Houston-area firms, understand the difference between general-purpose AI tools and specialized accounting platforms, and learn which skills your team needs to thrive alongside intelligent systems.
I’m Orrin Klopper, CEO of Netsurit, where we’ve guided over 300 client organizations through technology changes since 1995. Over the past three years, I’ve watched AI for accounting evolve from a buzzword into a core competitive advantage for firms that adopt it thoughtfully, and I’ve seen the mistakes that derail implementation when firms rush in without a clear strategy.
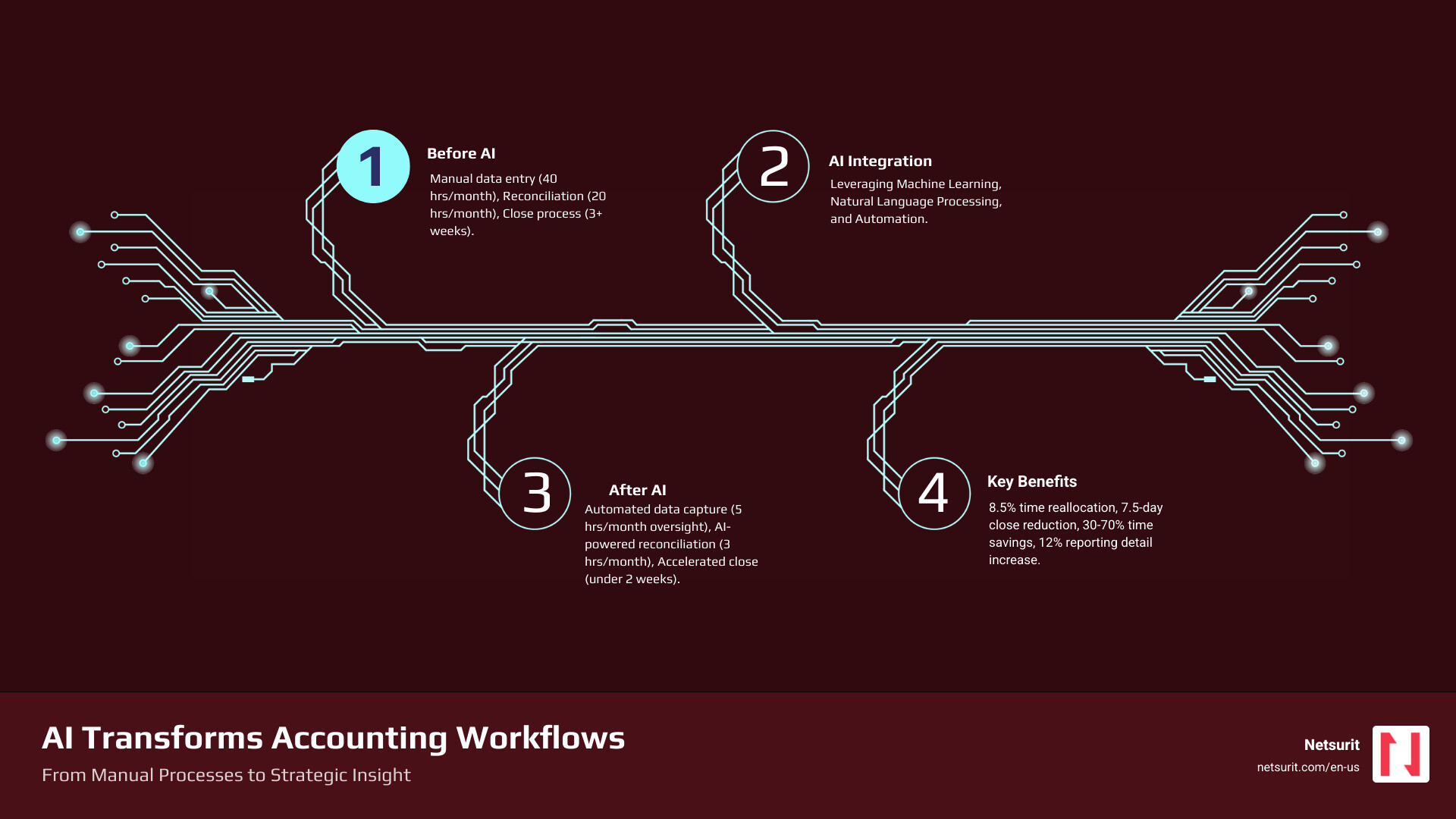
Infographic details: A visual flowchart showing how AI transforms accounting workflows. Left side shows “Before AI” with manual data entry (40 hours/month), manual reconciliation (20 hours/month), and manual close process (3+ weeks). Center shows “AI Integration” with icons for machine learning, natural language processing, and automation. Right side shows “After AI” with automated data capture (5 hours/month oversight), AI-powered reconciliation (3 hours/month review), and accelerated close (under 2 weeks). Bottom panel displays key metrics: 8.5% time reallocation to strategic work, 7.5-day reduction in close time, 30-70% time savings on workflows, 12% increase in reporting detail.
From Calculators to Cognition: What AI in Accounting Really Means
AI in accounting refers to systems that simulate human intelligence to perform tasks. This goes beyond simple automation to include learning, reasoning, and self-correction. The core technologies driving this shift are Machine Learning (ML), Natural Language Processing (NLP), and Generative AI, which are often packaged into specialized “vertical AI” solutions designed specifically for finance.
Machine Learning (ML) allows systems to learn from data without explicit programming, making it ideal for identifying patterns in large datasets—crucial for tasks like fraud detection and transaction categorization. Natural Language Processing (NLP) enables computers to understand, interpret, and generate human language, revolutionizing document review, contract analysis, and client communication. Generative AI (GenAI), a powerful subset of ML and NLP, can create new content, such as drafting reports, summarizing complex financial regulations, or even generating initial financial statements. Together, these technologies are moving accounting from a retrospective function to a proactive, predictive one.

General vs. Specialized AI
A key distinction exists between general-purpose AI like ChatGPT and specialized, or “vertical,” AI for accounting. While a general tool can draft an email or answer a basic query, it lacks the contextual understanding and domain-specific knowledge required for complex accounting tasks. A vertical AI solution, in contrast, is purpose-built for the finance and accounting industry. It understands the nuances of revenue recognition, lease accounting (ASC 842), and tax codes, ensuring compliance and auditability. As the a16z market map shows, venture investment is accelerating into these specialized tools that tackle accounting’s most complex use cases—from tax and audit to practice management, revenue recognition, and financial close.
Vertical AI solutions are trained on vast datasets of financial transactions, accounting standards, and regulatory documents. This specialized training allows them to offer better accuracy and fewer “hallucinations” (incorrect or fabricated information) compared to general-purpose models. When we discuss “agentic AI” in accounting, we’re often referring to these vertical solutions that act as intelligent agents, capable of autonomous task execution, learning from interactions, and adapting to firm-specific preferences. They can perform repetitive tasks, flag anomalies, and even generate insights, freeing up human accountants for higher-value work.
| Feature |
General-Purpose AI (e.g., ChatGPT) |
Vertical Accounting AI (e.g., Klarity.ai, Glean.ai) |
| Data Training |
Broad, web-scale data; diverse topics |
Specialized, finance-specific data; accounting standards, transactions, regulations |
| Compliance |
No inherent compliance knowledge; requires human input |
Built-in knowledge of accounting standards (GAAP, IFRS) and tax regulations |
| Auditability |
Outputs may lack source attribution; difficult to trace |
Designed with audit trails, source linking, and explainability for financial review |
| Accuracy |
Prone to “hallucinations” on specific domain questions |
Higher domain-specific accuracy; lower risk of errors in accounting contexts |
| Integration |
Often standalone; requires manual data transfer |
Seamless integration with ERPs, accounting software, and financial systems |
| Use Cases |
Content generation, general research, brainstorming |
Transaction categorization, reconciliation, fraud detection, tax preparation, audit |
Example: A Tale of Two AIs in Katy, TX
Consider a growing CPA firm in Katy, TX, that serves a diverse client base, from small businesses to mid-sized manufacturing plants. This firm uses a general-purpose tool like ChatGPT to help draft client communication templates and marketing materials for local outreach. It’s excellent for generating creative text and overcoming writer’s block.
However, for its core accounts payable (AP) work, which involves processing hundreds of invoices monthly for clients, the firm relies on a vertical AI solution like Glean.ai. This specialized tool integrates directly with their accounting software, uses ML to code invoices accurately, and automates the three-way matching process. When an invoice comes in for a client, Glean.ai automatically extracts relevant data, matches it against purchase orders and receipts, and flags any discrepancies. This ensures compliance, reduces manual errors, and provides a clear audit trail for every transaction—something a general-purpose AI cannot do with the required precision or auditability. The firm’s accountants in Katy then review flagged items, ensuring human judgment is applied where context is critical.
How AI Is Automating Workflows and Boosting Productivity Today
AI for accounting is not a future concept; it’s delivering measurable results now. A recent study confirms that accountants using AI reallocate approximately 8.5% of their time from routine data entry to high-value tasks like client communication and quality assurance. This shift is driven by AI’s ability to automate core accounting functions and provide deeper analytical insights. The 2025 Generative AI in Professional Services Report from Thomson Reuters found that vendors report time savings between 30–70% with AI-powered workflow automation. Furthermore, LLM-based research tools are helping to reduce document analysis time by 50% or more.

Key Applications and Gains
The impact of AI is seen across numerous accounting tasks:
- Task Automation: AI streamlines repetitive, rule-based processes, allowing systems to automatically categorize expenses, reconcile accounts, and even draft initial journal entries. Accountants using AI saw a 12% increase in general ledger granularity.
- Invoice Processing & Expense Management: Intelligent Document Processing (IDP) uses AI to extract data from invoices and receipts, automating data entry and matching, leading to significant time savings and reducing manual errors.
- Accounts Payable (AP) & Accounts Receivable (AR): AI automates AP workflows by matching invoices to purchase orders and receipts, and it can manage AR by sending automated reminders for outstanding invoices, significantly improving cash flow.
- Improved Analytics & Forecasting: AI analyzes large volumes of historical data to identify patterns and predict future trends more accurately than traditional methods. This improves financial forecasting, budgeting, and risk assessment.
- Fraud Detection: AI can identify unusual or anomalous transactions and patterns that indicate potential fraud, often with greater precision than human review, and at a much faster rate. The use of AI in antifraud programs is expected to triple over the next two years.
- Real-time Reporting & Anomaly Detection: AI provides continuous monitoring of financial data, flagging discrepancies or potential issues as they occur, leading to a 7.5-day reduction in monthly close time for firms embracing AI.
Example: Closing the Books Faster in Sugarland, TX
A mid-sized accounting firm in Sugarland, TX, serving local manufacturing clients, was struggling with a monthly close process that consistently stretched beyond two weeks. This delay limited their capacity to provide timely strategic advice to clients. After implementing an AI for accounting-powered close management tool, their workflow transformed.
The AI system now automatically reconciles thousands of general ledger transactions, flags anomalies in journal entries that might indicate errors or fraud, and generates draft financial statements in under two weeks—a process that previously took over three. This significant acceleration means the firm’s senior accountants can now dedicate their freed-up time to providing forward-looking cash flow analysis and strategic advice, strengthening client relationships and increasing advisory revenue. For firms in the Houston metro area looking to make a similar leap, a clear plan for technology adoption and IT strategy is essential. Our team at Netsurit can provide more info about IT strategy services to help you steer this transition.
Navigating the Risks: A Clear-Eyed View of AI’s Limitations
While the benefits of AI for accounting are compelling, adopting AI is not without its challenges. Implementation requires careful planning to address initial costs, potential skills gaps within your team, and the critical need for high-quality data. Integrating AI with existing legacy systems can be complex, and ensuring data cleanliness and readiness is paramount, as AI is only as good as the data it’s trained on. Furthermore, 62% of surveyed accountants express valid concerns about errors and accuracy in AI-generated reporting, highlighting the non-negotiable role of human oversight.
Ethical Guardrails and Human Oversight
The ethical implications of AI in accounting are a critical consideration. These include:
- Algorithmic Bias: AI models learn from historical data, which can inadvertently perpetuate biases present in that data. For example, an AI flagging transactions that unfairly targets specific business units due to learned biases rather than actual risk.
- Accountability: When an AI makes an error, who is accountable? Establishing clear frameworks for responsibility is essential.
- Data Privacy: AI systems process vast amounts of sensitive financial data. Ensuring robust data security and adherence to privacy regulations (like GDPR, if applicable to global clients, or state-specific privacy laws) is critical.
- Transparency and Explainability: Understanding how an AI arrived at a conclusion is vital, especially in audit and compliance. The “black box” nature of some AI models can be a barrier to trust and auditability.
- The “human-in-the-loop” model: This approach ensures that AI recommendations and automated processes are always reviewed, validated, and contextualized by a human expert. This maintains a critical balance between efficiency and accuracy.
- Judgment and Context: AI excels at pattern recognition and data processing, but it lacks human judgment, empathy, and the ability to understand nuanced business context. These remain indispensable human skills.
Trade-offs: Implementing AI for accounting
Implementing AI effectively means understanding its limitations and designing workflows that capitalize on its strengths while mitigating its weaknesses.
- Works best when: Automating high-volume, rules-based tasks like invoice processing, initial data extraction for tax returns, or first-pass bank reconciliations. These are the “laundry” tasks that free up human accountants.
- Avoid when: Making final judgments on complex tax strategies, ambiguous accounting treatments, or ethical dilemmas that require deep contextual understanding of a client’s business. These are the “poetry” tasks that demand human insight and creativity.
- Risks: Over-reliance on AI can lead to skill atrophy in human accountants if they stop performing basic checks. Data privacy breaches are a significant concern, especially if firms use unsecured public AI tools or don’t vet their vendors. Algorithmic bias can perpetuate historical errors or create unfair outcomes if not continuously monitored.
- Mitigations: Mandate a “human-in-the-loop” review for all critical AI-generated outputs, particularly those affecting financial reporting or compliance. Partner with a trusted IT provider for secure, private AI implementation and robust data governance. Regularly audit AI outputs for fairness and accuracy, and conduct algorithmic bias audits during AI development and post-deployment. Our team offers cybersecurity consulting to help firms in Houston, Sugarland, and Katy build these essential safeguards.
The Evolving Accountant: How to Thrive in an AI-Driven World
The most common question—”Will AI replace accountants?”—is the wrong one. AI will replace tedious tasks, not the professionals who perform them. The future belongs to accountants who partner with AI, using it to handle the “laundry” (data processing) so they can focus on the “poetry” (strategic advice and client relationships), a concept captured in a now-famous meme. A study from MIT Sloan found that experienced accountants used AI strategically to boost performance gains, highlighting that AI amplifies, rather than replaces, human expertise.
AI addresses the current talent shortage in the accounting profession not by eliminating jobs, but by making the profession more attractive and sustainable. By automating repetitive tasks, AI frees up accountants from burnout-inducing data entry, allowing them to focus on more stimulating, high-value work. This shift can help retain existing talent and attract new professionals seeking strategic, impactful careers.
Essential New Skills and Future Trends
To thrive in an AI-driven environment, accounting professionals need to cultivate a new set of skills:
- AI Literacy: Understanding what AI is, how it works, its capabilities, and its limitations. This includes knowing when and how to apply AI tools effectively.
- Prompt Engineering: The ability to craft precise and effective instructions for AI models to generate accurate and relevant outputs.
- Data Analytics and Interpretation: Moving beyond data entry to analyzing and interpreting AI-generated insights, identifying trends, and extracting actionable intelligence.
- Critical Thinking and Problem-Solving: Applying human judgment to AI outputs, identifying potential errors or biases, and solving complex problems that AI cannot.
- Client Communication and Advisory: Focusing on communicating financial insights clearly to clients, building strong relationships, and providing strategic advice based on AI-powered analysis.
Future trends indicate a move towards:
- Hyperautomation: The combination of AI, machine learning, and Robotic Process Automation (RPA) to automate increasingly complex end-to-end business processes.
- Agentic AI: Autonomous AI systems that can execute multi-step tasks, learn from experience, and adapt to changing conditions with minimal human intervention. Gartner forecasts that by 2028, 15% of daily accounting decisions will be made autonomously by AI agents.
- Real-time Audits: AI will enable continuous monitoring and analysis of financial data, making audits less about periodic sampling and more about real-time assurance.
- AI as a Strategic Advisor: AI will move beyond task automation to provide predictive and prescriptive insights, helping accountants guide clients on future financial decisions and risks.
Upskilling Pathways
To stay relevant and competitive, accounting professionals should proactively engage in upskilling. Here are some pathways:
- Certifications: Look for certifications in AI for finance, data analytics, or specific accounting software with AI integrations.
- Online Courses: Platforms like Coursera, edX, and LinkedIn Learning offer numerous courses on AI, machine learning, and data science relevant to finance.
- In-house Training: Advocate for and participate in internal training programs that focus on AI tool usage, prompt engineering, and ethical AI practices.
- Community Engagement: Join professional communities like the AI @ Thomson Reuters community to connect with experts, learn about the latest trends, and share best practices.
A Practical Guide to Adopting AI for Accounting Firms
Getting started with AI does not require a massive, high-risk investment. It requires a thoughtful, phased approach focused on solving specific problems and empowering your team. The CPA.com 2025 AI in Accounting Report outlines a roadmap: Find, Pilot, Operationalize, and Scale.
Step 1: Assess Readiness and Identify Pain Points
Before diving into solutions, understand your firm’s current state and where AI can make the biggest impact.
- Workflow Audit: Conduct a thorough review of your existing accounting workflows to identify high-friction, repetitive, or rules-based tasks.
- Repetitive Tasks: Pinpoint tasks that consume significant staff time but offer little intellectual challenge, such as data entry, invoice processing, or initial reconciliation. These are prime candidates for AI automation.
- High-Friction Processes: Identify areas where errors are frequent, compliance is challenging, or bottlenecks occur regularly.
- Data Hygiene: Assess the quality and structure of your data. AI thrives on clean, organized data, so addressing data hygiene issues is a crucial prerequisite.
Step 2: Start Small with a Pilot Program
Don’t try to automate everything at once. Choose a small, manageable project to gain experience and demonstrate value.
- Select Use Case: Pick 1-3 high-value, low-risk use cases for a pilot. Examples include AI-enabled bank reconciliations, automated expense categorization, or AI-assisted tax return review for specific forms.
- Assign Champions: Designate internal team members who will lead the pilot, learn the AI tool, and champion its adoption within the firm.
- Track KPIs: Establish clear Key Performance Indicators (KPIs) to measure the success of your pilot. This could include time saved, error reduction, increased client capacity, or improved turnaround time.
The market for AI for accounting tools is rapidly evolving. Selecting the right solutions and support is critical for success.
- Vendor Evaluation: Research specialized vertical AI solutions that address your identified pain points. Look for vendors with a strong track record, clear security protocols, and positive user reviews. Consider options like Klarity.ai for document review or BILL for AP/AR.
- Security: Prioritize solutions that offer robust data security, encryption, and compliance with relevant regulations. Ask potential vendors about their data usage policies and how they protect sensitive client information.
- Integration: Ensure the AI tool integrates seamlessly with your existing accounting software (e.g., QuickBooks, Xero) and other critical systems to avoid data silos and manual transfers.
- Scalability: Choose solutions that can scale with your firm’s growth and adapt to evolving client needs.
- Expert Partnership: Consider partnering with an elite tech partner like Netsurit. We help firms in Houston, Sugarland, Conroe, and Katy steer vendor selection, ensure secure implementation, and manage the ongoing IT infrastructure required for AI solutions. Our IT services for accounting firms are designed to support your firm’s technological evolution.
Step 4: Scale Thoughtfully with a Focus on People
Successful AI adoption is as much about people as it is about technology.
- Change Management: Communicate clearly and transparently with your team about the “why” behind AI adoption. Address concerns, highlight benefits, and involve staff in the change process.
- Upskill Workforce: Invest in continuous training for your team. This includes AI literacy, prompt engineering, and developing the critical thinking skills needed to work alongside AI.
- Create Accountability: Establish clear roles and responsibilities for managing and overseeing AI systems. Define who is responsible for AI outputs, error detection, and continuous improvement.
- Institutionalize Governance: Develop internal policies and a Responsible AI Framework that covers AI use, oversight, data management, and risk evaluation. This ensures ethical, secure, and effective long-term AI integration.
Frequently Asked Questions about AI for accounting
Will AI completely replace accountants?
No. AI automates tasks but improves the strategic, advisory, and relationship-building roles that require human judgment and empathy. It empowers accountants to deliver more value, not become obsolete. The focus shifts from transactional work to critical analysis, client communication, and strategic guidance.
How are the Big 4 using AI differently than smaller firms?
Big 4 firms like Deloitte and EY are investing heavily in proprietary, large-scale AI platforms for global audit engagements, risk assessment, and internal software development. They are building extensive in-house capabilities to handle their vast client bases and complex regulatory environments. For example, Deloitte has developed generative and agentic capabilities in its audit platform for initial document reviews, and PwC has seen 20-50% productivity gains in development processes due to GenAI.
Smaller accounting firms, in contrast, typically adopt specialized, off-the-shelf vertical AI tools. These solutions address specific pain points in areas like tax preparation, AP/AR automation, financial close, and practice management. They focus on leveraging accessible technology to improve efficiency and free up time for advisory services, rather than building bespoke AI systems from scratch.
What is the single most important factor for a successful AI implementation?
Data quality. AI is only as good as the data it learns from. Clean, structured, and well-governed data is the non-negotiable foundation for generating reliable and accurate AI-driven insights. Flawed or incomplete data will lead to biased or incorrect AI outputs, undermining the entire purpose of the implementation. Ensuring trustworthy data also involves ethical collection and careful management throughout its lifecycle.
Conclusion: Your Firm’s Next Move
AI for accounting is a transformative force, shifting accounting from a reactive, compliance-focused function to a proactive, strategic one. The first step is not a massive investment, but a strategic assessment of where automation can free your team to deliver higher value. By embracing AI thoughtfully, firms in Houston, Sugarland, Conroe, and Katy can not only overcome current challenges like talent shortages and manual errors but also open up new opportunities for growth and client engagement. As an elite tech partner, Netsurit helps firms securely implement AI solutions to crush downtime and open up business momentum, ensuring your technology strategy aligns with your business aspirations.
Get expert guidance on IT services for your accounting firm.